Welcome to CyberHygiene, my weekly newsletter, where I share tips and actionable data to help everyone stay safe online.
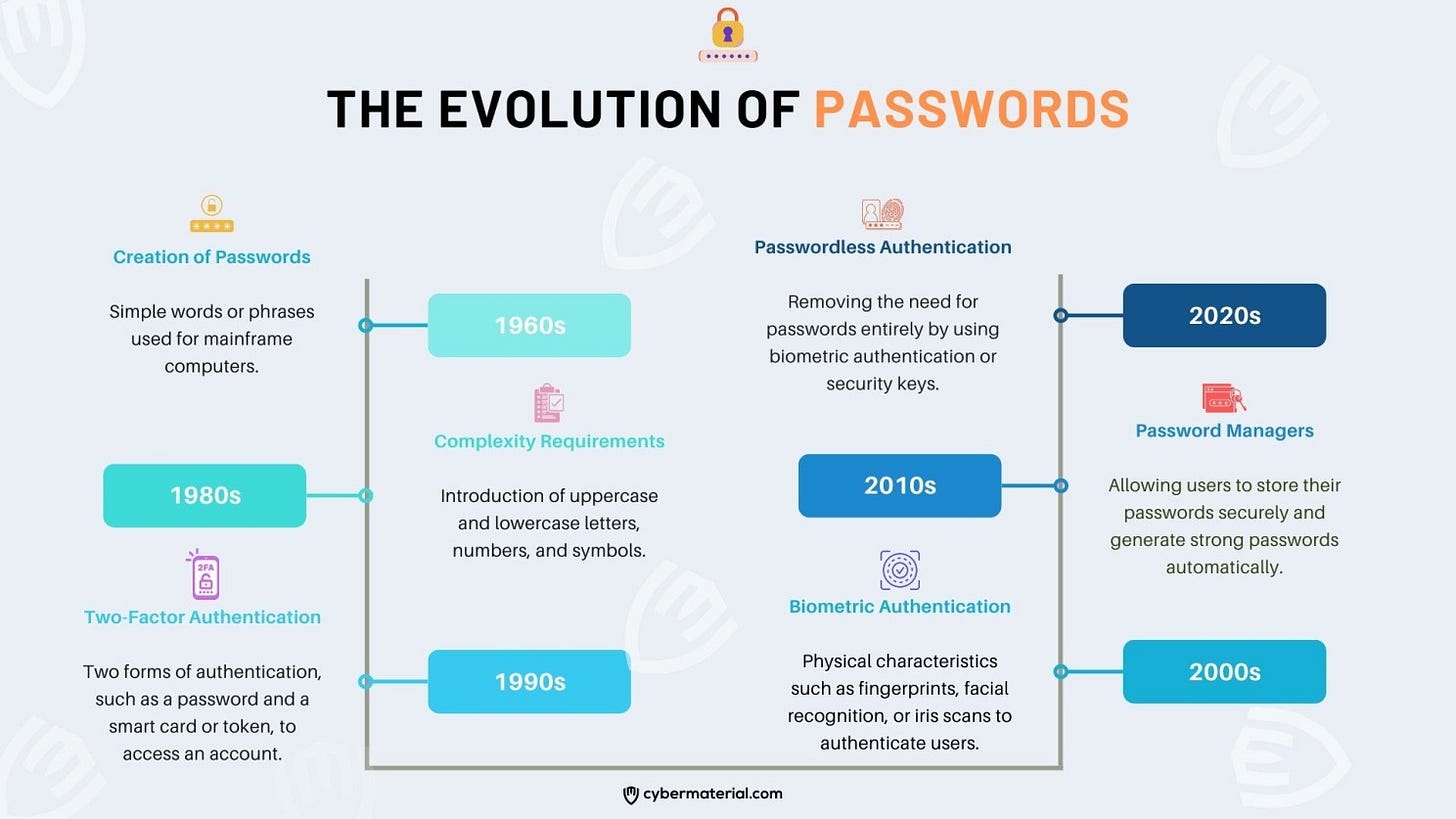
1. How have passwords evolved over time?
2. What are the top threats to passwords?
Cybercriminals can use software to crack passwords by guessing combinations of characters until the correct password is found. This is why it’s important to use strong, complex passwords that are difficult to guess.
Phishing and social engineering attacks are designed to trick users into giving away their login credentials by imitating a legitimate website or service. Once the cyber criminal has obtained the username and password, they can use it to access the account. For example, they may pose as a tech support agent and ask for the user’s password to fix an issue.
Keylogging is a method of recording every keystroke on a computer, including passwords. Cybercriminals can use keylogging software to steal login credentials without the user’s knowledge.
When a company or service experiences a data breach, it can result in user login credentials being compromised. Cybercriminals can use these stolen passwords to access the affected accounts.
Brute force attacks involve using software to try every possible combination of characters until the correct password is found. This method is time-consuming but can be successful if the password is weak.
4. What to do if your password is compromised or stolen?
Change your password immediately
Check for any unauthorized activity
Update your other passwords
Enable two-factor authentication (2FA)
Monitor your credit reports
Consider using a credit monitoring service
Be cautious of phishing scams
5. What resources are available to help you handle better your passwords and online credentials?
1) Books
Implementing Multifactor Authentication: Secure your applications from cyberattacks with the help of MFA solutions - by Marco Fanti
The 2023 Report on Multifactor Authentication: World Market Segmentation by city - by Prof Philip M. Parker Ph.D.
The 2023-2028 World Outlook for Multifactor Authentication - by Prof Philip M. Parker Ph.D.
Multifactor Authentication A Clear and Concise Reference - by Gerardus Blokdyk
The Zero Trust Framework: Threat Hunting & Quantum Mechanics - by Ravindra Das
Cloudifier mail and storage solution with single sign-on (SSO): One platform, many services - by Wassim Fares
2) Courses
3) Certifications
Certificate of Cybersecurity Awareness (CCSAP) - by 4MedPro
4) Documents
5) Podcasts