🚨 What happens when your vendor gets hacked?
It is no longer their problem. It is yours.
We used to think of breaches as a single company’s failure. The castle and moat model is obsolete. Your company’s security is now the sum of your entire vendor ecosystem’s hygiene.
And when one of those vendors falls, the domino effect can be staggering.
👉 30% of all breaches now involve a third party, a 100% increase from prior years.
The Financial Shockwaves
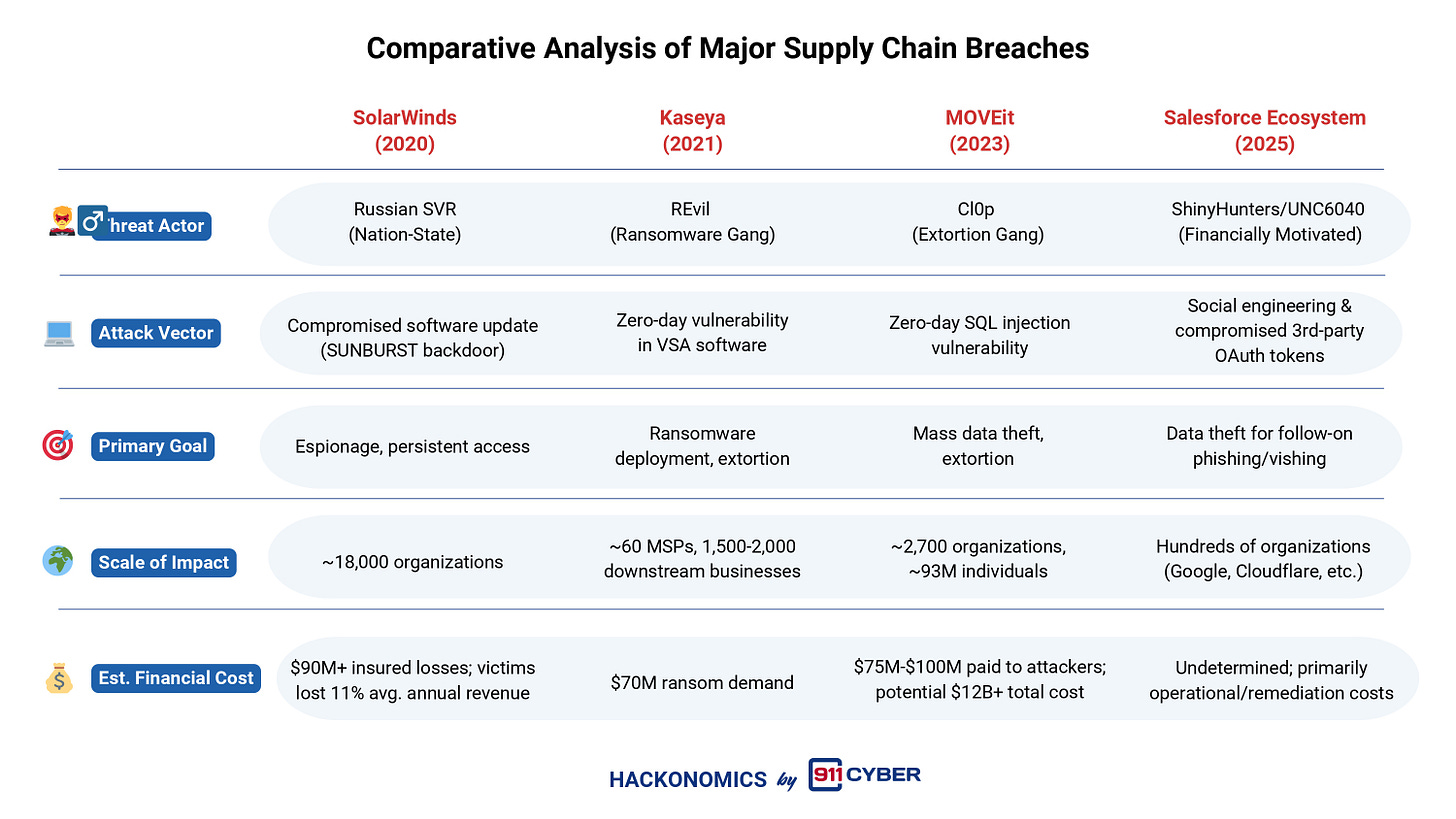
📉 SolarWinds (2020)
Not just a stock drop. A catastrophe. Impacted companies lost an average of 11% of annual revenue. The fallout was so severe that the SEC later fined victims like Mimecast and Unisys millions for failing to disclose the breach’s impact.
📉 MOVEit (2023)
A single file transfer vulnerability compromised more than 2,700 organizations and 93 million individuals. Attackers pocketed about 100 million dollars, while the global economic cost may exceed 12 billion dollars.
📉 Salesforce Ecosystem (2025)
Salesforce itself was not breached. Attackers hijacked OAuth tokens from third-party apps such as Salesloft and Drift. They stole business contact data that looked low risk, then weaponized it to launch highly credible phishing attacks against Google, Cloudflare, and others.
🔥 The Critical Insight for the C-Suite
You do not just inherit your vendors’ services.
You inherit their risk and increasingly their liability.
New SEC rules require disclosure of a material vendor-induced breach within 4 business days. Waiting is no longer an option. Annual questionnaires are not enough.
How to Manage the Domino Effect
✅ Integrate risk into procurement. Make Cyber Supply Chain Risk Management (C-SCRM) a mandatory part of vendor selection before a contract is signed.
✅ Embrace Zero Trust. Assume no user, system, or vendor is inherently trustworthy. Every connection must be continuously verified.
✅ Mandate contractual clarity. Contracts should include explicit security requirements, incident notification timelines, and audit rights.
✅ Integrate incident response. Incident response plans cannot live only in IT. They must include legal and finance from day one to meet that SEC disclosure clock.
The real question is no longer “Are we secure?”
It is “How resilient are we to a supply chain breach, and is our governance ready for the financial and legal fallout?”
💥 Vendor risk is not an IT problem. It is a direct threat to your bottom line and a core tenet of corporate governance.
Now, I would love your take:
- Should vendor risk be treated as a primary fiduciary duty on par with financial oversight?
- Should regulators enforce stricter vendor security standards across industries?
- Or is vendor risk too complex for one-size-fits-all rules?
Interested in the economics behind cybersecurity?